
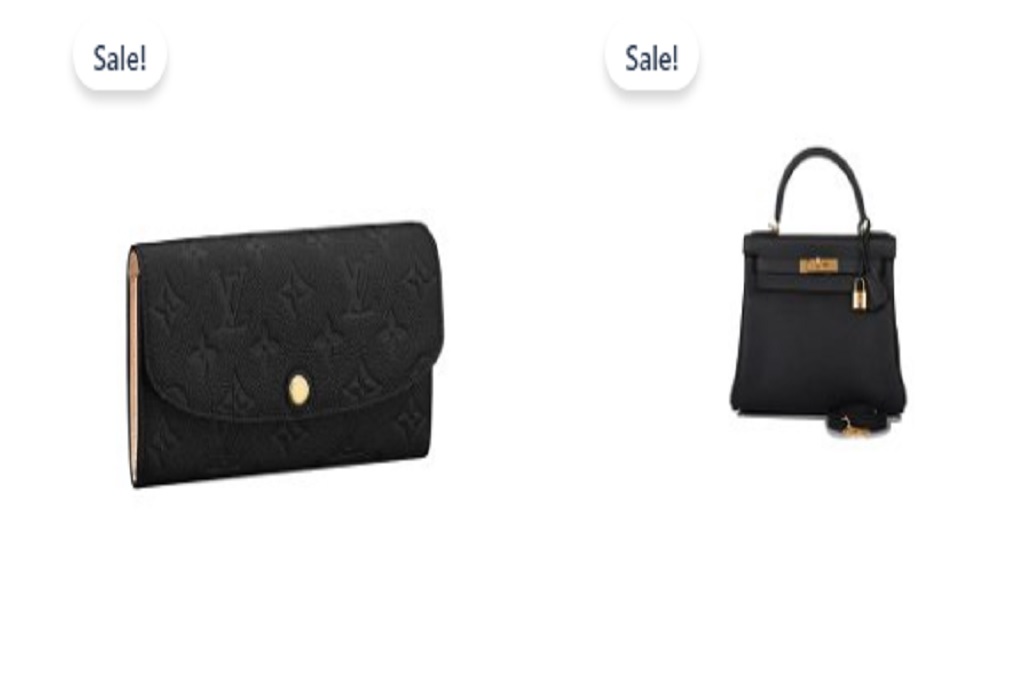
Cozycloudd Review {2024}: Is Cozycloudd store Legit or a Scam?
If you are looking for the Cozycloudd review, then you are here in the right place, as you were searching for the Cozycloudd store reviews to find out whether is […]

If you are looking for the Cozycloudd review, then you are here in the right place, as you were searching for the Cozycloudd store reviews to find out whether is […]
This Limber1574 page offers a wealth of information on the product and reliability of this website. To find out more about Limber1574 top, read our article in its full. In […]

This Niowatchted page offers a wealth of information on the product and reliability of this website. To find out more about Niowatchted com, read our article in its full. In […]
If you are looking for the Atoncehead review, then you are here in the right place, as you were searching for the Atoncehead com reviews to find out whether is […]

If you are looking for theCiasalesk review, then you are here in the right place, as you were searching for the ciasalesk.live reviews to find out whether is a ciasalesk […]
This Wildcurves page offers a wealth of information on the product and reliability of this website. To find out more about Wildcurves com, read our article in its full. In […]

This Petoxie page offers a wealth of information on the product and reliability of this website. To find out more about petoxie.com, read our article in its full. In this […]
If you are looking for the Kids-spot review, then you are here in the right place, as you were searching for the kids-spot.com reviews to find out whether is a […]

If you are looking for the Casyyay review, then you are here in the right place, as you were searching for the Casyyay com reviews to find out whether is […]

This Arenasportstore page offers a wealth of information on the product and reliability of this website. To find out more about Arenasportstore shop, read our article in its full. In […]